Note: this isn’t our normal fare on WUWT, but we do occasionally carry political pieces. What makes this interesting is that Steve McIntyre (ClimateAudit) is involved in researching it. -Anthony
Guest Essay Leo Goldstein, Science for Humans and Freedom Institute
The CrowdStrike Con
CrowdStrike is the network security company, that was called by the DNC when it suspected a breach in its network in early May of 2016. CrowdStrike announced that there were at least two breaches by “two separate Russian intelligence-affiliated adversaries” — Fancy Bear (APT28) and Cozy Bear (APT29). CrowdStrike even suggested that Fancy Bear belongs to GRU (Russian military intelligence) and Cozy Bear belongs to FSB (Federal Security Service, replacement of KGB). The DNC was satisfied with CrowdStrike service and refused to let the FBI examine its servers, surprising even James Comey. All data and alleged malware samples that were given to the FBI, CIA, NSA, DNI, other security companies, and the public came from CrowdStrike. There is something fishy in this, isn’t it? Especially when we learn that
In my opinion: CrowdStrike is a fraud
From its beginning in 2012, CrowdStrike has been using fraudulent attribution methodology to attract publicity, to confuse customers, and to alarm potential customers. Alarmism and fraud were hallmarks of Obama’s administration. CrowdStrike’s close relationship with the Obama administration, especially FBI Director Robert Mueller (until 2013), and rotating door between them ensured not only impunity, but quick success. CrowdStrike was valued at $3B in the last investment round, and closed around June 16.
Since around 2005, corporations and government agencies faced a new kind of cyberthreat: external intrusions into their networks followed by data theft. Technological solutions have failed. The intrusions usually started when hackers obtained some insider’s password or tricked a user into installing malware on his or her computer inside of the network. Malware components are frequently the same or similar, because hackers sell code to each other and frequently open source it. The hackers are caught only rarely. A hacker anywhere in the world can use an intermediate computer anywhere else in the world. The Obama administration had other priorities than securing U.S. networks.
Volunteers and security companies classified hackers’ methods and malware families. In 2011, Dmitri Alperovitch, a former VP of threat research in McAfee, came up with a trick. He announced: “You don’t have a malware problem, you have an adversary problem.” He claimed that advanced malware families are unique to hacker groups, and that the hacker groups can be identified by the kind of malware they use. This was a false statement. Alperovitch doubled down by claiming that he could identify a foreign government behind most intrusions. Thus, he moved the discussion from the technical realm into the political one. In his first attribution he pointed finger at China. Later, Alperovitch even claimed to know which unit of PLA had committed intrusion, and the DOJ indicted its officers!
It was patently absurd and Alperovitch had to struggle. He started one company, then joined the board of another one until he met a person who fell for his trick: Shawn Henry. He was the executive assistant director to Robert Mueller, who appointed him in 2010. By that time, Mueller already had a solid track record of incompetence and self-service: he missed 9/11 and botched an anthrax investigation, but mastered the use of “process crimes” against white collar defendants (such as Martha Stuart), and created a cachet of FBI cadres personally loyal to him. In March 2012, Mueller’s appointee Shawn Henry retired from the FBI to join Alperovitch and George Kurtz in CrowdStrike. With such connections, the business was booming. Shawn Henry is current president of CrowdStrike Services & CSO.
Alperovitch also became a media star. When a big data loss is announced, nobody wants to listen to technical details. People want to know whodunnit. Honest cybersecurity experts did not know. Alperovitch claimed he did and was always able to point a finger at the governments of China, Russia, Iran, or North Korea. Some of these attributions might have been accidentally correct. It is possible that CrowdStrike clients liked this approach as well. Being hacked by China or Russia sounds better than being hacked by an unknown guy in the Bahamas or some other exotic location. Of course, CrowdStrike was embraced by the Obama administration, and enjoyed all the perks that came from this embrace.
Alperovitch did not make a secret of his method. When CrowdStrike encountered a new type of malware, the first thing it did was a national attribution, which was reflected in the name of the group, and alleged having exclusive possession of it. For example, alleged Russian groups were given a name ending with Bear. Thus, the national attribution is made first and could not be changed no matter how much contrary evidence accumulates later.
The revolving door between CrowdStrike and Obama administration also deserves mention. For example, Steven Chabinsky, a Deputy Assistant Director of the FBI Cyber Division under Robert Mueller, was hired by Crowdstrike in September 2012. He became CrowdStrike’s general counsel and chief risk officer. On April 13, 2016, he has been appointed by Obama to the Commission on Enhancing National Cybersecurity (press release). It was two or three weeks before the DNC invited CrowdStrike to investigate and/or to make a cover story of the DNC data leak.
The Hillary Campaign
Note that the date when CrowdStrike was called in and other factual details differ between the stories told by CrowdStrike in 2016 and by the DNC in a lawsuit filed on April 20, 2018 (Democratic National Committee v. the Russian Federation, General Staff of the Armed Forces of the Russian Federation … Donald J. Trump for President Inc. …). The date was May 6 according to CrowdStrike and April 28 according to the DNC. This is how dumb the Democratic Party became; not surprising that it has selected Michael Mann as the climate advisor and Dmitri Alperovitch as the cybersecurity advisor. According to CrowdStrike, within 10 seconds its software “found” the culprit. The lot fell on the Russian government.
The DNC was unmoved. It knew that Putin preferred Democrats to Republicans. The Obama administration had just accommodated Putin’s unprovoked aggression against Ukraine. Putin annexed the Crimean Peninsula and occupied the most industrially developed areas of Ukraine without much reaction from the U.S. Compare that to the U.S. reaction in 2008 when Russia clashed with Georgia after the latter shelled Russian forces there. George W. Bush sent a destroyer with “humanitarian aid,” which I think was an overreaction. Trump promised, and proved, to be a stronger president than Bush. Hillary was not just accommodating to Russia. On the photos of Hillary and Putin together, she looks like his girlfriend. Not to mention Uranium One and other love stories.
Hillary knew that Putin would hold her back. On June 14, 2016, the DNC coordinated a Washington Post article about a security breach in the DNC and a simultaneous publication of alleged technical details by CrowdStrike. Both laid blame squarely on the Russian government. The Russian government denied responsibility, as expected. The WaPo article claimed that no donor information had been accessed and only a few documents had been stolen, including an opposition research on Trump. The next day the mentioned opposition research was posted on the web by somebody calling himself Guccifer 2.0.
When journalists looked at this document they discovered an error message in Russian. The fifth estate (acting more like the fifth column) wrote that that was a proof that the Russian government had been behind the intrusion. The ultra-sophisticated GRU hackers made a mistake by copying and pasting the content of the original file on a computer with default Russian language settings! The journalists writing on the subject did not give a thought to the fact that Russian is the native language to tens of millions of people outside of Russia. Those who did probably decided not to write about it at all.
The opposition research file with “Russian fingerprints” might had been forged by the DNC or CrowdStrike and fed to the purported hackers with two purposes: to bring attention to the content (i.e., smears) against Trump, and to prove the “Russian connection.” That suggests that somebody involved (in the DNC or CrowdStrike) did not believe in the Russian connection from the beginning.
By its own admission, CrowdStrike watched over the activities of two teams of alleged Russian government hackers from May 6 until early June. Such behavior doesn’t make sense. Even given the infinite trust Hillary had in Putin, the DNC’s IT department should have shut down the Internet connection immediately, then changed all passwords and sanitized all computers. Apparently, in 2016 Obama’s friends felt they didn’t need to make their lies believable. If somebody didn’t believe, it was his problem.
But the only meaningful question is who released the DNC’s dirty laundry to the public, not whether the DNC had been hacked, by whom, or how many times. Some think the documents were originally leaked by DNC staffer Seth Rich, who was later murdered. The first document dump had a bad surprise for the DNC – files with the names and other information of the donors. Something went not according to plan.
Between June 18 and July 14, Guccifer 2.0 published multiple documents from the DNC network, and these documents were doing real harm to Hillary. At this point, even somebody trusting CrowdStrike would understand that the documents were not coming from the Russian government. Remember how Russia released the eavesdropping recording from the U.S. Embassy in Ukraine, following 2014 invasion of Crimea? It posted a single recorded conversation between the top U.S. diplomat for Europe Victoria Nuland and the Ambassador to Ukraine Geoffrey Pyatt on YouTube, then used a third party to bring attention to that video. The advantages of a small release: no risk that the important document gets lost among many unimportant ones; the sources and methods are less likely to be compromised; other documents remain hidden for future use, and the target is kept in dark about the extent of the data loss. The bulk release is typical of individual leakers or hackers. The DNC probably cultivates atmosphere of blind trust, because Hillary seemed to continue believing that Russia had leaked those documents.
Hillary felt betrayed by Putin. Hell hath no fury like hers. Hillary and the Democratic Party started accusing Russia and Putin of all thinkable and unthinkable crimes, attempting to re-start the Cold War with a single purpose – to remain in power. That brings to mind the words of one of the largest Democrat donors and climate alarmists Tom Steyer in an interview with Rolling Stone: “Maybe we can have, like, a nuclear war and then we get a real course correction.” Two years have passed, but who knows how long they’ve been dreaming about a nuclear war. Before Trump, Steyer was equally obsessed with carbon dioxide.
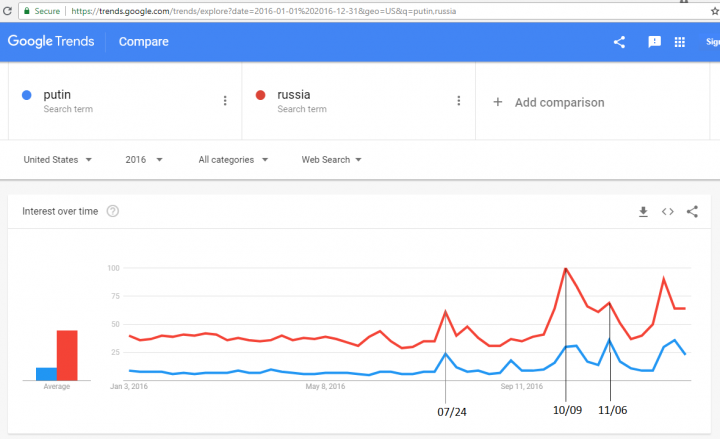
Within less than six months from July to December 2016, the electronic media, joined at the hips with the DNC, entirely rewrote the history of Hillary-Putin relationships. Even many conservative writers forgot that Hillary started to malign Russia and Putin in July 2016 after the alleged hacking and leaking of the DNC documents. Hillary had excellent relationships with Putin before the leak. The DNC leak caused Hillary’s hostility towards Putin and Russia, not the other way around. That’s easy to see with Google Trends, as shown below.
The “consensus” around the DNC leaks attribution was manufactured through circular reasoning. CrowdStrike published samples of malware, which it had allegedly found on the DNC servers, and some security firms supported its baseless attribution claims to scare up some business and to stay in good grace with putative winners of future elections. Later, Obama’s cadres in the DNI, CIA, and FBI used the same compromised data to compose an intelligence community assessment, falsely claiming that the Russian government interfered in the 2016 elections against Hillary. An unclassified version of it has been published on January 6, 2017. The FBI and CIA expressed high confidence in the assessment, but the NSA distinguished itself by expressing only moderate confidence.
Steve McIntyre Weighs in
Steve McIntyre performed some analyses and wrote about the DNC leak in ClimateAudit. I cannot express it better, so I quote:
https://climateaudit.org/2017/09/02/email-dates-in-the-wikileaks-dnc-archive/
Yesterday, Scott Ritter published a savage and thorough critique of the role of Dmitri Alperovitch and Crowdstrike, who are uniquely responsible for the attribution of the DNC hack to Russia. Ritter calls it “one of the greatest cons in modern American history”. Ritter’s article gives a fascinating account of an earlier questionable incident in which Alperovitch first rose to prominence – his attribution of the “Shady Rat” malware to the Chinese government at a time when there was a political appetite for such an attribution.
There were no fewer than 14409 emails in the Wikileaks archive dating after Crowdstrike’s installation of its security software. In fact, more emails were hacked after Crowdstrike’s discovery on May 6 than before. Whatever actions were taken by Crowdstrike on May 6, they did nothing to stem the exfiltration of emails from the DNC.
Isn’t it fun to work with a security company like this? I couldn’t care less what security companies the DNC uses to secure its own network, but Obama’s administration gave CrowdStrike government contracts. It also allowed countless leaks of confidential information from supposedly secure government networks – hardly a coincidence.
https://climateaudit.org/2018/03/24/attribution-of-2015-6-phishing-to-apt28/
In two influential articles in June 2016, immediately following the Crowdstrike announcement, SecureWorks (June 16 here and June 26 here) purported to connect the DNC hack to a 2015-6 phishing campaign which they attributed to APT28. …
Attribution of the phishing campaign to APT28 was therefore done on the basis of infrastructure connections. But while there is an infrastructure association to APT28 but there is also an association to a prominent crimeware gang.
APT stands for Advanced Persistent Threat. APT28 is Fancy Bear.
https://climateaudit.org/2017/10/06/whiskers-on-software-part-1/
In Crowdstrike’s original announcement that “Russia” had hacked the DNC, Dmitri Alperovitch said, on the one hand, that the “tradecraft” of the hackers was “superb” and their “operational security second none” and, on the other hand, that Crowdstrike had “immediately identified” the “sophisticated adversaries … I draw the contrast to draw attention to the facial absurdity of Crowdstrike’s claim that the tradecraft of the DNC hackers was “superb” – how could it be “superb” if Crowdstrike was immediately able to attribute them?
In fact, when one looks more deeply into the issue, it would be more accurate to say that the clues left by the DNC hackers to their “Russian” identity were so obvious as to qualify for inclusion in the rogue’s gallery of America’s Dumbest Criminals, criminals like the bank robber who signed his own name to the robbery demand.
To make matters even more puzzling, an identically stupid and equally provocative hack, using an identical piece of software, had been carried out against the German Bundestag in 2015.
Bundestag fire!
https://climateaudit.org/2017/10/10/part-2-the-tv5-monde-hack-and-apt28/
“Re-reading the two stages of contemporary articles, the first analyses of malware, linking back to malware known in Arabic language forums, to IP addresses in Iraq and Algeria and to jihadi-sympathizing hackers, are much more specific than the subsequent analyses attributing the hack to APT28, which did not present a single technical detail (hash, IP address etc.) It is also frustrating and troubling that the proponents of APT28 attribution did not discuss and refute the seemingly plausible connections to jihadi sources. It is also troubling that so much emphasis in contemporary discussion of FireEye’s analysis incorrectly associated the Cyrillic characters previously described by FireEye in October 2014 with the TV5 Monde incident.
Second, the confidence of attribution to APT28 was dramatically aggrandized in subsequent reporting, fostered in part by inaccurate original reporting. Contrary to newspaper reports, Trend Micro did not attribute the seizure of TV5 facilities to APT28. Its assessment was indeterminate, weakly preferring that the seizure was separate from APT28 eavesdropping.”
https://climateaudit.org/2017/10/02/guccifer-2-from-january-to-may-2016/
“To my eye, there is convincing evidence that G2 actually hacked Democrat Party computers from at least January 2016 on. This is inconsistent with Adam Carter’s theory that G2 was a false flag operation by Crowdstrike and the DNC – the metadata points to too early a start to support such a theory. G2 metadata also points too early for G2 to be a false flag by Fancy Bear/APT28 who are said to have gained access only in April 2016.”
See more at https://climateaudit.org/?s=crowdstrike and https://climateaudit.org/?s=guccifer.
Details
History Rewriting
The following Google Trends graph shows the ratio of Google searches for Putin and Russia over time. The number of searches is a proxy for the ratio of mentions in the media. The media was totally on Hillary’s side. She controlled the media narrative on Russia and Putin. The red line for Russia stays low in the range of 30-40% from the beginning of 2016 until the week of July 24. Discovery of the data leak is not noticeable. Even announcement of DNC hacking by Russia on June 14 coincides with only little bump for Russia searches. The lines for both Putin and Russia go up on the week of July 24, after Hillary became angry with continuing publication of the leaked documents and decided to connect Putin to Trump, and to malign them together. From the early October until after the elections the searches for Russia and Putin stay at abnormally high level. Searches for Putin reach peak on the election week, starting at November 6.
Anybody can search MSM websites and see many articles from August – November of 2016, alleging that Trump is associated with Putin and that Hillary would “hold Putin accountable” for something.
Note also that John Brennan made a friendly visit to his colleagues in Moscow in March 2016. That shows that neither the Obama administration nor Brennan considered Russia an adversary at that time. Just few months later, all hell had broken loose. The article The Kremlin Really Believes That Hillary Wants to Start a War With Russia (Foreign Policy, September 7, 2016) is a reminder:
“If Hillary Clinton is elected president, the world will remember Aug. 25 as the day she began the Second Cold War.
In a speech last month nominally about Donald Trump, Clinton called Russian President Vladimir Putin the godfather of right-wing, extreme nationalism. To Kremlin-watchers, those were not random epithets. Two years earlier, in the most famous address of his career, Putin accused the West of backing an armed seizure of power in Ukraine by “extremists, nationalists, and right-wingers.” Clinton had not merely insulted Russia’s president: She had done so in his own words.
Worse, they were words originally directed at neo-Nazis. In Moscow, this was seen as a reprise of Clinton’s comments comparing Putin to Hitler. It injected an element of personal animus into an already strained relationship — but, more importantly, it set up Putin as the representative of an ideology that is fundamentally opposed to the United States.
… To Russian ears, Clinton seemed determined in her speech to provide this missing ingredient for bipolar enmity, painting Moscow as the vanguard for racism, intolerance, and misogyny around the globe.
The nation Clinton described was unrecognizable to its citizens. Anti-woman? Putin’s government provides working mothers with three years of subsidized family leave. Intolerant? The president personally attended the opening of Moscow’s great mosque. Racist? Putin often touts Russia’s ethnic diversity. To Russians, it appeared that Clinton was straining to fabricate a rationale for hostilities.
…
That fear [that Hillary might attempt a “regime change” in Russia] was heightened when Clinton surrogate Harry Reid, the Senate minority leader, recently [August 30, 2016] accused Putin of attempting to rig the U.S. election through cyberattacks. That is a grave allegation — the very kind of thing a President Clinton might repeat to justify war with Russia.”
At that time, Putin might have switched his preference from Hillary to Trump. Russian officials probably expressed such preference unofficially — exactly as Hillary wanted. That doesn’t mean Putin was aiding Trump. The Russian government should have thought there was a change in American policy, largely independent of who would win elections. Everyone was sure Hillary would win. Putin did not have a chance to change that. It would be unwise for Putin to even attempt – almost inevitable failure would earn him shrill retaliation, and almost impossible success would only make the adversary stronger. But the show was probably convincing enough even for honest intelligence officers.
Relationships with Russia were already bad in September, but that wasn’t enough for Democrats. To support Hillary, the Obama administration (with John Kerry as Secretary of State) turned minor disagreements with Russia into a conflict. October 12, 2016, CNN:
“It’s not a new Cold War. It’s not even a deep chill. It’s an outright conflict.
US-Russia relations have deteriorated sharply amid a barrage of accusations and disagreements, raising the stakes on issues ranging from the countries’ competing military operations in Syria, disputes over Eastern European independence and escalating cyber breaches.
Washington publicly accused the Kremlin of cyberattacks on election systems and the democracy itself last Friday. That came after talks on a Syria ceasefire broke down as US officials suggested Russia be investigated for war crimes in the besieged city of Aleppo. Moscow has steadfastly denied that it’s meddling in the US presidential election. … Democratic presidential nominee Hillary Clinton has pointed to the hacks as evidence that Russia favors her GOP opponent, Donald Trump. Appearing at an investment forum in Moscow on Wednesday, Russian President Vladimir Putin dismissed that charge. … Meanwhile, Moscow abruptly left a nuclear security pact, citing US aggression, and moved nuclear-capable Iskandar missiles to the edge of NATO territory in Europe. Its officials have openly raised the possible use of nuclear weapons.
And that’s just the highlight reel.”
At the time, the MSM attributed that confrontation to Russian military activity in Syria. In fact, the Democratic Party was fanning flames of war to stay in power. Besides the Democrats’ obscurantism, obsession with political power, and “by any means necessary” attitude, much of this madness has been driven by puny conmen like Michael Mann and Dmitri Alperovitch.
Attribution Fallacies
Attribution of sophisticated network intrusions to specific actors is universally accepted as a very difficult problem. CrowdStrike and similar “solutions peddlers” usually build their case on a chain of very weak assumptions. Russia is home to some of the most sophisticated computer hackers in the world. The first target on which they try their exploits is Russian banks. Their skills and malware code become available to the Russian government when they are caught, or even before that. But they are also available to anybody in the world ready to pay cash. The following parameters and assumptions cannot be used for attribution of intrusions to specific actors.
A) Malware Origin
- Malware is frequently attributed to Russia because Russian words or Cyrillic fonts are found in it, or in earlier versions of it. But Russian is the mother language for many people born and living in Ukraine, Belarus, Kazakhstan, Estonia, Latvia, and Lithuania, and tens of millions of emigrants all over the world, including the U.S.
- An even more stupid and incompetent attribution attempt is the use of malware compilation time and finding that malware has been compiled at the working hours (like 8am to 6pm) for Moscow. In fact:
- Software compilation and build can be scheduled for any time.
- Software companies do builds either continuously or overnight.
- Programmers and hackers rarely work at traditional 9-to-6 schedules.
- Computers building malware can be set to any time, language, and country settings.
- Russia spans eleven hourly time zones, so almost any time is working hours somewhere in Russia.
There is nothing easier for a sophisticated hacker group than to build malware on a computer with Russian settings and/or other Russian fingerprints to lead investigators astray. An analyst sees what a sophisticated adversary wants him to see.
B) Targets
Theoretically, in some cases it’s possible to make an attribution of hacking with certain malware type to a specific government based on the attacked targets. This approach was used to allege that malware from APT28 and APT29, allegedly found on the DNC network, belongs to the Russian government because it was used in the past to attack its targets of interest. But this claim is based on data cherry-picking. The same malware was known to attack all kinds of targets, from banks to national Olympic committees. The majority of reported targets were in Russia. Russia attacks Russia – how foolish is that? Wide range of targets demonstrates activities of multiple hacking groups, some of which possibly working for governments. Security researchers engaged in attribution typically make their mind up early, and then look only at the cases that confirm their hypothesis. Security companies are interested only in attacks on large or rich organizations that can be convinced to purchase their services, and such organizations are easy to declare to be of interest to Russia. Most cyber-attacks are not reported at all. But even the cherry-picked list of incidents suggests that the attribution is incorrect.
C) It’s hard to believe that a government-backed hackers’ group would be using the same malware for years, long after it had been detected, analyzed, and publicly attributed to it. Here, I mean that malware remains the same even after enhancements and modifications – if it can be identified as a derivative of the original. I would expect any such group to continuously develop new and more effective “products” that bear no resemblance to the previous ones. At least, they can change existing code to remove the published identifiers. CrowdStrike and few copycats presumedly tracked APT28 and APT29 from 2008.
D) Circular referencing and bandwagon effect.
The MSM frequently alleges that the “DNC hack” has been confirmed by multiple private security companies, and then by the Intelligence Community Assessment (ICA) from January 6, 2017. In fact, all these confirmations based on data from the same source – CrowdStrike. Some companies and government agencies also relied on its analysis. Other companies jumped on the train with similar flawed attribution methodologies – a bandwagon effect. Actual reports from companies other than CrowdStrike included limitations, qualifications, conditions, and/or limited confidence in the findings. Of course, these nuances were lost in the general media coverage. The readers and viewers were left with wrong impression that all these assessments were independent and unconditional. After ICA publication, cybersecurity companies started to refer to ICA as the ultimate source of authority. In fact, even Obama’s request for ICA was highly prejudicial, demanding “intelligence report assessing Russian activities and intentions in recent U.S. elections.” Thus, Obama has already decided that significant “Russian activities in recent U.S. elections” had taken place, and the intelligence agencies were requested to elaborate on the thesis. Some say that ICA was prepared in violation of existing rules, and was unduly influenced by John Brennan, who had been acting against Trump since at least August 2016. (https://americaoutloud.com/u-s-intelligence-communitys-contrived-intelligence-assessment/)
The following is an example of a circular evidence trail by a security professional and a corporate officer who does agree with the attribution of the DNC leak to Russian government:
Difficulty Level – EXTREME: Why is attribution such a challenge?
“When I was serving in cybersecurity in the Department of the Defense, the main lesson I learned was that you can never truly achieve a high-level of confidence in who is attacking you without the triangulation of multiple intelligence sources.
… when you look closely at the evidence that both of these outstanding organizations found in their investigations, they could all potentially be ‘false flags,’ planted by an advance targeted threat actor emulating the capabilities of these supposed Russian actors.”
So what switched him from skepticism to alarmism?
“… the public case made that Russian influence is behind the activity at the DNC has a few holes, but our government, on both sides of the political aisle, seem to be very sure of that conclusion. Based on sheer faith, I will take our government at its word …”
That’s it – sheer faith! The sheer faith is supported by an analysis made by SecureWorks and ICA, which used purported evidence received from CrowdStrike. The sheer faith leads him to affirm the initial detection and attribution by CrowdStrike. BTW, the Republican side of the aisle is represented by Senator Burr, RINO-NC.
Most attribution theories cannot be tested. In the science, such theories are called unfalsifiable, and, therefore, unscientific. But in one rare case, CrowdStrike theory alleging Russian hacking of Ukrainian howitzer control software has been checked – and found false. CrowdStrike retracted its claims in this specific case without any other consequences.
John Brennan, Obama’s CIA Director
The January 2017 assessment makes heavy emphasis on supposedly superb “sources, tradecraft, and analytic work” used by the FBI and CIA. But the words of John Brennan show a different picture.
Brennan Delivers Remarks at the Center for Strategic & International Studies Global Security Forum 2015:
“When CIA analysts look for deeper causes of this rising instability, they find nationalistic, sectarian, and technological factors that are eroding the structure of the international system. They also see socioeconomic trends, the impact of climate change, and other elements that are cause for concern. Let me touch upon a couple of them.
…
Mankind’s relationship with the natural world is aggravating these problems and is a potential source of crisis itself. Last year was the warmest on record, and this year is on track to be even warmer.
Extreme weather, along with public policies affecting food and water supplies, can worsen or create humanitarian crises. Of most immediate concern, sharply reduced crop yields in multiple places simultaneously could trigger a shock in food prices with devastating effect, especially in already fragile regions such as Africa, the Middle East, and South Asia. Compromised access to food and water greatly increases the prospect for famine and deadly epidemics.”
This passage demonstrates traitorcraft rather than tradecraft. Sources are replaced by UN agencies’ policy papers and analytic work is replaced by credo quia absurdum. But James Clapper is even worse.
James Clapper, Obama’s DNI Director
James Clapper appears clean before his appointment as DNI Director in 2010. For six years, Clappers signed the Statement for the Record on the Worldwide Threat Assessment of the US Intelligence Community for the Senate Select Committee on Intelligence. In Obama’s second term, Clapper started including in them the alleged climate change threat. Climate change was mentioned:
2014 statement (Clapper): once
2015 statement (Clapper): 4 times
2016 statement (Clapper): 8 times, including the following passage:
“Environmental Risks and Climate Change
Extreme weather, climate change, environmental degradation, related rising demand for food and water, poor policy responses, and inadequate critical infrastructure will probably exacerbate—and potentially spark—political instability, adverse health conditions, and humanitarian crises in 2016. Several of these developments, especially those in the Middle East, suggest that environmental degradation might become a more common source for interstate tensions. We assess that almost all of the 194 countries that adopted the global climate agreement at the UN climate conference in Paris in December 2015 view it as an ambitious and long-lasting framework.
- The UN World Meteorological Organization (WMO) report attributes extreme weather events in the tropics and sub-tropical zones in 2015 to both climate change and an exceptionally strong El Niño that will probably persist through spring 2016. An increase in extreme weather events is likely to occur throughout this period, based on WMO reporting. Human activities, such as the generation of greenhouse gas emissions and land use, have contributed to extreme weather events including more frequent and severe tropical cyclones, heavy rainfall, droughts, and heat waves, according to a November 2015 academic report with contributions from scientists at the National Oceanic and Atmospheric Administration (NOAA). Scientists have more robust evidence to identify the influence of human activity on temperature extremes than on precipitation extremes.
- The Paris climate change agreement establishes a political expectation for the first time that all countries will address climate change. The response to the deal has been largely positive among government officials and nongovernmental groups, probably because the agreement acknowledges the need for universal action to combat climate change along with the development needs of lower-income countries. However, an independent team of climate analysts and the Executive Secretary of the UN climate forum have stated that countries’ existing national plans to address climate change will only limit temperature rise to 2.7 degrees Celsius by 2100.”
This asinine opinion, attributed to the intelligence community by James Clapper, adds injury to insult by referring to UN bodies four times, each time taking them as sources of authority.
The following statements were made by Clapper in person at Intelligence and National Security Alliance (https://www.insaonline.org) conference in September 2016 (https://archive.is/J32Hm):
“In the coming decades, an underlying meta‐driver of unpredictable instability will be, I believe, climate change. Major population centers will compete for ever‐diminishing food and water resources and governments will have an increasingly difficult time controlling their territories.”
“Well, I alluded to that briefly in my remarks, and I do think climate change is going to be an underpinning for a lot of national security issues. The effect on climate, which drives so many things ‐‐ availability of basics like water and food, and other resources, which are increasingly going to become matters of conflict, and already are, between and among countries. And so this is going to give rise to national security insight that we’ll need to understand this and hopefully help anticipate it. So I think climate change over time is going to have a (inaudible) effect on our national security picture.”
Thus, James Clapper lost his mind and/or integrity even before he gave DNI approval to CrowdStrike claims. He continues leveraging climate alarmism to against national security — https://climateandsecurity.org/tag/james-clapper/.
Remarks
Frauds like CrowdStrike were common under Obama’s administration. Theranos, a purported blood testing innovator, raised more than $700 Million between 2011 and 2017 and was valued at $9B at some point. In 2011, the Theranos founder recruited George Shultz, a Secretary of State in Reagan administration and currently “a senior statesman with a climate solution,” as a board member. He brought on more high level political figures. Theranos’ founder Elizabeth Holmes even secured support from Bill Clinton. She also wanted to save the planet from climate change! Theranos never had a working product, technology, or even competent R&D, but politics easily prevailed over technology and science in those years. Investment poured in, Walgreens signed a contract and built in-store booths for Theranos’ blood tests. In 2015, Obama’s FDA approved the non-existent Theranos’ blood testing device! Fortune wrote that Ms. Holmes, a university drop out, was an inventor in 26 patents issued to Theranos. Today, Theranos’ fraud is revealed, but Ms. Holmes walked away with hardly a slap on the wrist.
Google (Alphabet) is an investor in CrowdStrike, having participated in at least three investment rounds in 2015, 2017, and June 2018. Google fails to disclose this and other conflicts of interest in search results related to the companies in which it invests.
Google, Facebook, and Twitter had an opportunity and incentives to use their knowledge and experience in cyber security to explain to the public and Congress the folly of the Russian attribution of the DNC leak and related conspiracy theories when they were called to testify before Congress. They had access to the same information that I do, and Google also had insider’s information about CrowdStrike. Nevertheless, they chose to lie to Congress and the public, and put their weight behind the conspiracy theories, even to the point of accepting a partial blame for the alleged “Russian” actions.
In 2011, Dmitri Alperovitch founded Asymmetric Cyber Operations LLC. Then he joined the board of CounterTack, a cybersecurity firm. MSM usually omits these details of his career.
In February 2017, CrowdStrike sued testing company NSS Labs, apparently to prevent the publication of the NSS Labs test results for a CrowdStrike product. The lawsuit was dismissed.
Following the apparent success of the CrowdStrike fraud, other security companies started to make dubious attributions. Examples are FireEye (FYEY) and SecureWorks (SCWX). When describing APTs, SecureWorks advices incorrectly to “Focus on the ‘who’ not the ‘what’.” For most organizations, the question who is unhelpful, because the answer is anybody or everybody. The network security should be able to handle a threat from anybody, proportionally to the value of the information on the network. This is the same as in the physical security. We don’t ask who when we lock the doors. We lock the doors to protect against all thieves, rather than asking who.
Alperovitch is a fellow of Atlantic Council. I don’t think this is a major factor – his motives are financial gain, and, possibly, media attention.
Here, the word hacker is used in its common meaning — somebody who accesses computer systems without authorization. Initially, it meant something like a darn good programmer, especially in the Linux community.
Other sources of data and analysis of the DNC leaks:
Opinion:
Disclosure
I hold short positions in (bet against) the Google stock.
Other reading
- Jeffrey Carr, The DNC Breach and the Hijacking of Common Sense, June 19-21, 2016
“Attribution is hard enough without cybersecurity companies picking the evidence they need to support the conclusion that they want with threat actor models that are completely devoid of common sense. We can do better.”
- Jeffrey Carr, Faith-based Attribution, July 10, 2016
“It’s important to know that the process of attributing an attack by a cybersecurity company has nothing to do with the scientific method. Claims of attribution aren’t testable or repeatable because the hypothesis is never proven right or wrong.”
“When it comes to cybersecurity estimates of attribution, no one holds the company that makes the claim accountable because there’s no way to prove whether the assignment of attribution is true or false unless …”
- Jeffrey Carr, FBI/DHS Joint Analysis Report: A Fatally Flawed Effort, December 2016
“A common misconception of “threat group” is that refers to a group of people. It doesn’t.”
“Unlike Crowdstrike, ESET doesn’t assign APT28/Fancy Bear/Sednit to a Russian Intelligence Service or anyone else for a very simple reason.”
“In fact, the source code for X-Agent, which was used in the DNC, Bundestag, and TV5Monde attacks, was obtained by ESET as part of their investigation!”
- Bitdefender, APT28 Under the Scope, 2015
“We have reasons to believe that the operators of the APT28 network are either Russian citizens or citizens of a neighboring country that speak Russian.”
The emphasis is mine. Attacked countries, in the decreasing order of vulnerabilities according to the report: Ukraine, Spain, Russia, UK, Romania, Bulgaria, US, Canada, Portugal, Italy, and Mexico. Why would Russia attack Russia?
- Forbes, Security Advice From The CEO Of The World’s Newest Unicorn – CrowdStrike, May 2017
CrowdStrike CEO George Kurtz about their attribution of the alleged DNC breach: “That work raised our profile considerably, solving a high profile problem, separating us from a crowded field in the security space.”
Given such stunning success, it is quite natural that CrowdStrike doesn’t want to admit to the fraud in their detection and attribution!
“Crowdstrike became one of the most famous brands in the cybersecurity industry last year after securing a contract with the Democratic National Committee.”
“At the start of 2014, President Obama assigned his trusted counselor, John D. Podesta, to lead a review of the digital revolution, its potential and its perils. When Mr. Podesta presented his findings five months later, he called the internet’s onslaught of big data ‘a historic driver of progress.’”
What a joke!
Thanks for publishing. Very important.
Thank you
Thank you
There’s an odd New Zealand angle to this : Podesta was phished from a Tokelau address. Tokelau is a New Zealand territory. Yes it’s easy to get an address in Tokelau but New Zealand is part of Five Eyes (the US-Australia-NZ-UK-Canada signals intelligence/ survelliance alliance), so it’s hard to believe they don’t know who the Podesta phisher was.
Hug? How do you know where the server was? Do you have an IP?
Or do you believe that any domain name placed under a ccTLD (country code Top Level Domain) has both its NS (name server) and Web server in that specific country?
No. And yes. There is a New Zealand, (and Australian) angle, but…
Podesta was apparently phished from IP 134.249.139.239 (Ukraine, kyivstar.net broadband) It’s a *mobile* broadband provider, so potentially a physical mobile phone.
They chose this provider because previously that year some base-stations of Kyivstar in Donbass had been seized by Russian separatists. So they were trying to imply a Russian controlled operation. BUT the location of that IP is not in the separatist areas.
Then we have the Registration of DCLeaks. It’s to a privacy service registered to PO Box 16, Nobby Beach, Queensland Australia. It really is a physical PO box. It’s the registration address of thousands of dodgy sites (like the Muslim Brotherhood). That’s the final registration. The original one (2012, maybe 2010) was to Ronald Vanyur of Huntington Beach California.
The New Zealand angle is the SOA (Start of Authority) for actblues[.]com, which is claimed to be implicated in the DCCC hack. The SOA gives fisterboks[@ur momisugly]email.com and nameserver ititch[.]com which is 103.6.212.252 in New Zealand.
Also links to Malaysia, France, and of course USA.
But not Russia.
The site
https://defycccc.com/
does not seem to exist.
Also, a search for Science and Humans Freedom Institute doesn’t bring up any hits.
Try https://defyccc.com
Things are starting to make sense now, thanks!
Shows that changes in government democracies is crucial for the search for the truth In a one party system the truth doesn’t exist.
That’s why, even though I am Republication, I am worried about the seeming death wish of the Democratic party. If they keep on with their stupidity there will (effectively) be only one party in this country, and that is very bad.
PATTON sez:
“That’s why, even though I am Republication,
I am worried about the seeming death wish of the Democratic party.”
It’s REPUBLICANS you are a member of,
not Republications?
and the other party is the DEMO-CRAPS,
er, I mean the DEMOCRAT party,
not the “Democratic” party.
The Democrats are acting so dumb,
with their love of socialism,
and their wish for open borders,
they make Trump sound like a
diplomat and a genius.
The link should be
https://defyccc.com/
It had one too many ‘c’s in it as posted.
The other one has a page come up in Bizpedia – just that they are a Delaware registered corporation.
Revised quote:
“Being hacked by China or Russia sounds better than being hacked by some 12-year-old geeky kid from his parents’ basement.”
Being hacked by Russia is better than having a 27-yr old Bernie supporter DNC staffer, disgusted by the obvious bias against Bernie in the DNC, come forward as the DNC insider hack source.
It never was a “hack”. The initial DNC release just before primary which Clinton rigged, came from a leak. Assange has clearly stated that the material came from a leak and not a hacked source.
Exactly. It makes it sound like the it takes the resources of a shady government department to crack your security rather than a slightly soft cheeseball.
Ah, it’s Ari Halperin, or at least that’s what he called himself here in the past:
https://wattsupwiththat.com/2016/07/21/ooops-not-al-31-scientific-societies-actually-signed-the-aaas-consensus-letter/
He managed to run the headline here “Ooops! Not all 31 scientific societies actually signed the AAAS ‘consensus’ letter”, on the basis of nothing more than the fact that not everyone he wrote to responded to his questions.
Yeah well… I’d take anything this guy says with a grain of salt.. or a few million grains possibly.
#1 It’s Leo Goldstein, where did you see Ari’s name?
#2 It’s not ‘nothing more’, but I think Ari was getting wrong what ‘signed’ means these days.
#3 Ari’s piece was very educative. The signatories felt threatened.
#4 bon appetit
I wouldn’t bother with “Philip Schaeffer” or whatever he calls himself. It appears to be a trollbot. I don’t think the bot actually read the most excellent article it linked to.
He’s a real person, I’ve conversed with him, however his viewpoints posted here are indeed often bot-like.
But Anthony, the “screed” should have been edited better to try to keep down, the leaps of faith.
“#1 It’s Leo Goldstein, where did you see Ari’s name?”
From the byline of one of his articles here
“Leo Goldstein researches and writes about climate alarmism, and its interconnection with other social ills. Until recently, Leo Goldstein wrote under the pen name Ari Halperin.”
Yes, and he has written here under the name Ari Halperin in the past, which I find interesting given what Anthony says about anonymous cowards.
I’d love to see you guys try and identify a real bot. That would be hilarious in comparison to what I write.
Yeah, I know, it’s just a throwaway insult, but it is pretty dumb.
Has it been made clear to the readers of WUWT Ari and Leo are the same person so that they know they are hearing from the same person when they read articles here under either name, or did the names just change discretely?
[yes, Mr Goldstein requested that WUWT change his name from the pen name “Ari Halperin” to his real name “Leo Goldstein” -mod]
Aaaaaaand, I’m on moderation. Lol. Touched a raw nerve there I think.
(There is nothing in the Mod Bin showing it) MOD
well, i just got the same waiting for moderation message again.
edit: Nope, gone this time. One of the messages I just posted is still gone. I got the same message, waiting on moderation.
I think someone else might have got a bit annoyed with me. To moderation, then disappeared.
I think there might be two hands at work here, not knowing what the other is doing.
For a few mins there everything was going to moderation, now it’s back to normal.
The message you just responded to got that awaiting moderation message, and didn’t show up immediately.
You know that, but did the readers of WUWT ever get told that the articles here by Ari Halperin are actually by Leo Goldstein?
Sorry, I think my last comment disappeared. He told you, but did you tell the readers of WUWT so they would know that articles here under the name Ari Halperin are actually by the same Leo Goldstein who wrote this article?
I mean, it seems to be news to some of them, like they heard it for the first time from me. So, did WUWT tell it’s readers who he really was, or just change the names without informing readers of what happened?
“yes, Mr Goldstein requested that WUWT change his name from the pen name “Ari Halperin” to his real name “Leo Goldstein””
I didn’t ask if he told you. I asked if you have informed your readers so they know who they were reading under the name Ari Halperin, and that it was actually the same person as they are reading now, Leo Goldstein?
[Mr. Goldstein made a statement some time back to that effect. You seem to be the only person concerned about it -MOD]
Sigh, the path of conversation would be a lot clearer without that bout of moderation in the middle to confuse things.
That some of the message above can’t be edited any more, but ones further above them still can is proof that moderation was happening. Any comment on that?
[Sometimes comments get flagged by wordpress. If you don’t want to have the occasional inconvenience then simply don’t comment and take that risk. -MOD]
“[Sometimes comments get flagged by wordpress. If you don’t want to have the occasional inconvenience then simply don’t comment and take that risk. -MOD]”
Lol, it’s OK. I’ll accept that it was just coincidence that all my messages suddenly went to moderation in the middle of a discussion that may annoy some people at WUWT. And that some of them stayed missing, and that one of the mods seemed to have a different idea of what was going on than the other.
I didn’t ask if he has ever stated anything about his name change. I didn’t ask if he told you about the name change. I asked if you have ever informed your readers of this. Did he make his statement here? After all, you are now carrying articles from him under two different names. And that on a site with a strong position against anonymous cowards.
Putting his real name on his last article here would be a good start. But that’s just my opinion 🙂
I have to admit, I’m a little surprised that I’m the only one here who cares given the scorn put on anonymous cowards round this place.
[Mr. Halperin makes it clear he uses a pen name, and he makes it clear on his website defyccc.com that he posts articles at WUWT and gives their titles and links. He’s put a defyccc.com in every story I’ve seen. Seems to be much ado about nothing on your part. -MOD]
OK, I can let it go, but can you please actually answer the question. Why bother replying to me twice with answers to other questions, but not the one I asked? Anyway, up yo you if you answer, as I have now been told to drop it, and we all know what happens next if you don’t.
[“we all know what happens next if you don’t.” Is that some sort of threat? -MOD]
A threat? I can’t put anyone on permanent moderation, or ban them. That’s what happens to people here who don’t drop issues when told to.
[Mostly it happens to people who are rude and insulting, and/or use expletives, and violate the published blog policy. https://wattsupwiththat.com/policy/ Thread bombing is one of the things that can earn permanent moderation. -MOD]
Look, I’m happy to let this slide, but there would be three less posts from me if you’d just said “No” when I asked if you told your readers about the name change. And less posts again if moderation hadn’t complicated things.
As far as I’m concerned, so long as people here know they are the same person (and from some of the comments they obviously didn’t), then it’s all good and I need say no more.
[Thanks, as mentioned earlier, Mr. Goldstein made a statement about it here. Not every commenter may have read it. We have no control over that -MOD]
Thanks, Phil. Sixteen posts and (clutch pearls tightly, now) moderation because you refuse to do your own research about what can or can’t be found here. Your future posts will give me a chuckle as I recall this string of clutched pearls.
Mr. Schaefer is in fact a concern troll. He has a long history of whining about the way he thinks WUWT should be run. He simply doesn’t like this website, so tries to tear it down. In reality he’s little more than an ankle biter.
He rails about this one issue, because that’s all he’s got.
Funny though, he never demands name accountability from other blogs, like his Australian mate “Sou” at Hotwhopper who NEVER uses her real name Miriam O’Brien… when she writes derogatory and defamatory posts….mostly about me and other people who publish here. Mr. Schaefer’s OK with that sort of behavior under pen names…apparently, because we never see him at that website trying to tell Ms. O’Brien how bad that sort of behavior is.
Mr. Schaefer had been on permanent moderation at WUWT because nearly his entire comment history consisted of trying to tell everybody how WUWT should be run according to his viewpoint. The rest were just jabs. AFAIK, he
hasn’t contributed anything positive to any discussion here. When I switched to the new server, I wiped the slate clean, that included him.
Some people have returned to their typical patterns, others have learned from their past bad behavior and have cleaned up their act.
We often get over 1000 comemnts a day, most go through with no issue, some get flagged moderation, some end up in the trash because they look like spam or have links to websites that are dangerous. The wordpress server flags comments regularly and the moderation staff and I have to clear valid comments regularly. It happens to everybody who regularly comments here. Grousing about it doesn’t help.
And I’m not even sure Philip Schaefer is his real name. Given the way he preaches here, it could be a nom de plume. For all I know, he could be Miriam O’Brien, trying to stir the pot here so that she can get choice comments to frame derogatorily at her HotWhoppette website…its what she does, and she’s become essentially an Internet stalker of me personally. Someday, Ms. O’Brien will be in for an ugly legal surprise.
Mr. Schaefer (if that is your real name) if you want to go back on permanent moderation, keep doing what you’re doing to the point of it becoming what would be considered thread bombing.
If you want to get along in this community, try another tact. Your choice, but bear in mind that in my policy page, I reserve the right to refuse service to anyone. I’m not required to post your comments.
Mr. Schaefer, there’s no need to respond. I’m not interested in a discussion with you. Good day sir (or madam).
“Grousing about it doesn’t help.”
Grousing is the American way !
I love it when people use uncommon words
like “grousing” or “whippersnapper”
or “lollygagging”.
Also, after criticizing someone online,
one should always close with:
“Have a nice day”.
paul courtney said:
“Thanks, Phil. Sixteen posts and (clutch pearls tightly, now) moderation because you refuse to do your own research about what can or can’t be found here. Your future posts will give me a chuckle as I recall this string of clutched pearls.”
I was told:
“[Sometimes comments get flagged by wordpress. If you don’t want to have the occasional inconvenience then simply don’t comment and take that risk. -MOD]”
So, nothing to do with what research I did or didn’t do. WordPress has no comprehension of such things.
But I can’t really talk to you about is because that can then be used as a reason to put me on permanent moderation. Yah know, thread bombing and all.
Philip Schaeffer
So after posting dozens of comments in a row, AKA “thread bombing”, and complaining that the VOLUNTEER moderators are not immediately approving your next steaming pile of … words … now you are whining that you “can’t really talk” about some random thing for fear of being put on permanent moderation???
Gotta say, I’m astounded that Anthony has been generous enough to allow you another chance. And I’m even more amazed that, having been given such a second chance, you are doing your very best to get put back on permanent moderation.
Me, I’d have planted your face in the pavement after about the eighth useless comment in a row, but then I’m a semi-reformed cowboy, and Anthony is a gentleman … however, even he has his limits.
My advice? Stop talking about process, about moderation, about how long it takes for your comments to appear, about people who don’t care about your dumb questions … and start talking about the ISSUES UNDER CONSIDERATION. You know. Like the rest of us do.
Your endless whining is unseemly …
w.
The extent and damage caused by computer hacking is exaggerated IMO.
The media is a willing participant in the hype.
And they always first interview experts from security companies who obviously want to talk it up, to increase business for themselves.
Jeff, the extent of the per se “hacking” of Hillary Clinton’s unprotect basement “server” is not only un-exaggerated, ….. it is the worstest case ever of US secret and/or classified data/info being easily accessible to any programmer, anywhere on earth, with “smarts” enough to access it.
Hillary’s unprotect basement “server” was an “open door” to hundreds of other government “servers”, …… to anyone that wanted to “get in”.
According to testimony at a congressional hearing, at least one foreign actor was able to download almost every email Hillary had on her illegal server. Louis Gomert said the unnamed hacker had transferred all but about 10 of Hillary’s emails to another location.
It’s a pretty good bet that if one foreign actor was able to get into Hillary’s server, then others probably did, too.
So at least one of our foreign enemies has a full set of Hillary’s deleted emails.
How secure is your setup if a phishing ploy can manage to hack into it? Answer: It’s not secure at all. Lamebrains!
No-one actually used the email information to harm the US.
“while some of the emails contained information that the government considered classified to the highest levels, the information was “innocuous” and not “particularly sensitive” because the emails discussed matters that were simultaneously available in the public domain—such as in newspapers”
Jeff – July 13, 2018 5:45 pm
Jeff, why do you persist in making such asinine and silly statements?
GETTA clue, …… Jeff, …… given the fact that it was Hillary’s “private server” and situate in her private residence ………. then you can “bet you last $100 that her hubby Bill, … daughter Chelsea, ….. son-in law, ……along with a dozen or so other relatives, friends, etc., …….used that same server for their IP address for connection their PC’s, I-phones, etc. to the Internet ……. because it wouldn’t cost them a single penny to do so ………… and that was an equally IMPORTANT reason why Hillary et el had to smash her I-phones, I-pads, etc., ……. plus delete everything off of the “server” storage before she would let any ”outsider” have access to said server.
Don’t forget, Bill Clinton was “making cash deals” with foreign entities, …… the same as Hillary was doing.
Cyber crime is a $1.5 trillion industry.
You are totally wrong.
The cybersecurity vendors exaggerate how much their products and services help, and also the focus on what cyber risks people and businesses should focus on, but the problem is enormous and undisputed.
“Cyber crime is a $1.5 trillion industry.”
For the “cybersecurity vendors” yes probably.
Real attribution is very rarely possible if you are dealing with an experienced attacker.
The problem is that computer messages do carry an awful lot of metadata describing their origin and path to the recipient. In the early days of computer security this was used to convict people – and the attackers learned rapidly. So nowadays this metadata will routinely be spoofed, and passed through zombied machines to disguise the real point of origin.
Of particular interest is the ability to trace-route IP packets. If a police force can access all the jumps a packet has taken, they should be able to find the originator. So an obvious response is to route a malicious attack through machines under the jurisdiction of a government hostile to your victim – because then the victim’s police force will probably not be able to get permission to examine those machines.
For example, if I were to attack the WUWT web site from a site in Boston, I would be very likely to be traced rapidly. If I were to route the attack through a machine in France, it would take longer for the FBI to contact the French Sûreté Nationale, but eventually a trace would go in.
However, if I were to route through North Korea, it’s unlikely that the US authorities would get any co-operation. However, it’s probably quite difficult to zombie a NK machine. Russia and China would be the obvious choices – and they have the benefit that no US authorities will look any further, because blaming Russia and China is very politically acceptable…
Very interesting. Yes, its hard to say who’s behind anything these days, and 97% likely that who your are led to believe is, isn’t….
Long off topic stream of consciousness
…Interestingly the last part of the article touches on security experts being at the least naïve about climate change – but this is something that has happened over the last 50 years in a general way.
Two centuries ago all educated people had probably had very similar educations. Since then human knowledge of the written kind and skill sets of the academic kind have mushroomed, and today there is little chance that even a very well educated person has – for example – both in depth understanding of Internet sand IT security and a solid background in say the history of Thailand, or the ability to speak Estonian (which is by the way the language of Estonia, mostly).
This is what leads to the terribly embarrassing spectacle of Experts in one field making dumb fools of themselves in another, It also leads to some serious political chicanery.
Because today people think that because they have reasonably high IQs and have been to one of the increasingly dumbed down Universities’ their <beliefs and their received wisdom carry greater weight than the opinions of the ordinary man, and this gives them the right, if not the duty, to press on regardless of the opinions of the plebs.
Sound familiar?
And this is the problem. Received wisdom does not make you wise. Merely full of other people’s knowledge. What makes you wise is the ability to go back to first principles and check that knowledge against the data for yourself, until you know that it can be trusted – and that is of course what we regular readers here like to do. Check out received wisdom to see if it is, not to put too fine a point on it – utter bunk.
So I personally like to read an article I understand, rather than one covered in reference to learned papers that I cannot.
However there are a lot of people – especially in the Left, who will never admit that they do not really understand, and be humble enough to go back, cudgel their brains and try and learn enough of a new discipline to actually go back to enough first principles to validate or invalidate a particular claim. Peer review is supposed to cover that, but scientists are no longer adversarial with each other. Everybody needs the job and publishing papers is how you keep it. A tacit agreement not to trash a colleagues paper means he will support yours in due course.
So the appeal to authority – the expert – and the authentication of that expert by peer review, that used to carry some weight, is now no more than the monkey-talk of Kipling’s bandar log. Consensus Truth – “We all say so, so it must be true”.
And in academia at least that has been amplified by the way in which salaries and careers are tied to government grants, and the publishing of papers in journals. Western academia today is socialist because it’s funded by government. And it cannot afford to contradict the government too far.
All these facts are conducive to the development of a sort of socialised world view that is a-scientific. People have to have a picture of the world to operate against, and that picture is now controlled at the government end by public sector employment, and at the media end by commercial forces. It by and large doesn’t have to be true, just plausible. And if it appeals to the ego, and flatters the insecurities of a lot of people who have qualifications that in another agee they would not, its going to be so much more successful…at selling a political position or a product.
I don’t know what to do about this. In my life, born just post WWII – there was a lot of honesty back then, and huge respect for the ‘boffins’ who had created jet aircraft, radar, and we much later discovered, the digital computer.
All that vanished at the end of the cold war. Lacking an existential threat, who needs intelligent people? Smart people went into banking or marketing or politics to make money for themselves, not to protect their nation. Or do science.
So ‘boffins’ became second or third rate brains (or in Mann’s case 4th rate) whose desire to acquire that respect was unmatched by their ability to deserve it. And there is no test of their quality save the accolades of equally incompetent peers. Ships will not go down, aircraft will not crash, because e.g. Mann Got It Wrong.
And as I pointed out, critical review is something few can do. If they have the intellect, they may not have the understanding and the toolset. And even fewer will want to do, if it threatens their income.
Where this leads me, is not a place I want to go. I understand, I think why we have all this incompetence everywhere, why huge swathes of otherwise moderately intelligent people believe in stuff, that they have been told, that is dangerously wrong, but extremely useful to those promulgating the message. Because no situation has arisen where possession of such a view means they die before procreating!|
Darwin rules, OK?
Summer time, and the living is easy, so why not daydream yourself into a fantasy?.
Or is winter coming?
If Nature throws us a curved ball and we are too stupid to catch it…goodnight Vienna.
The smart ones will survive and be respected…
In Idiocracy, a man smart enough arrives and is respected. If no one smart arrives, society collapses. Joseph Tainter’s interesting work ‘the collapse of complex societies’ posits a hypothesis that societies that start off by exploiting a particular ecological or sometimes political niche, organise and develop structures to maximise the benefits of these niches and then fail because as the resource runs out or the political situation changes they have no response but ‘more of the same’ – more bureaucracy, more structure, more organisation – when sometimes what works better is to go back to first principles – say peasant farming – and start again. Or at least that is all they are capable of.
Isn’t that the Green position – ¨We can’t cope with technology, we want to go back to being hunter gatherers” – tacit admissions that they are in fact too stupid to live in an advanced technological society, and it scares them?
Then we have those in between, who have competency but not universal competency, which is where we came in. The astrophysicist who knows models, but nothing about climate, who endorses climate change, The biologist, who knows a lot about life, but not a damned thing about models or statistics. Or the geologist, who knows a lot about past CO2 and temperature and cries ‘foul’ but is shouted down because he knows nothing about models or climate.
IN comfortable times when it doesn’t matter, BS will flourish. BS leads to people not being competent to meet external events. Lack of competency to meet external events leads to general lowering of standards of living until the people get upset and somehow randomly select leaders until they find one with some degree of competency, laud him and thereby recover. Or they don’t and go down before the barbarians who are at least competent at being barbarians.
In other words stupidity and incompetence and groupthink are natural things. It is only necessary for most people to know how to procreate. And no one likes Cassandras. Only when the chips are down do we value the competent and the super competent. And generalised incompetence leads eventually to the chips being down.
It is rather like climate. Being stupid dumb and comfortable is where we want to be, but being stupid dumb and comfortable means the tiger can creep up on us, and then we need to suddenly get smart , kill the tiger, and relax into being stupid dumb and comfortable all over again. But the tiger has killed the dumbest ones.
Its a negative-feedback-with-lag system. Just like climate, and such systems are only quasi stable and are somewhat chaotic.
So I think – i hope – we are just about to pass Peak Stupidity. What comes next is a harder set of times for people where they need to get smarter. If they do, OK. If they don’t. Bye bye Kansas.
Apologies for that. But beyond all the stuff that gets covered here, I ponder what the pattern is. The pattern of social and psychological ideas and tensions, that could lead to someone tasked with national security being so mistaken about stuff outside his remit.
If only all grabbermints could force-feed their citizens Ritalin. But like Pravda, the fake-news-gushing MSM is the next best thing.
+100
Leo Smith,
Your synthesis is the closest I have read to my own ruminations, thank you.
It gives a credible alternative to the conspiracy theory ridicule that sceptics suffer but I don’t consider plausible. These patterns of thought contagion you describe are common. They do not need an exceptional topic like global warming to make them happen.
A present concern I have here in Australia is about the nature and quality of the people selected by some unclear process to represent Australia in places like international policy forums. In our military we have a senior officer recently retired and seeking media, who has been through sex change. Or main rep at the Paris climate fest has also just been through sex change. His/her friends are unusual if you search the Net and speculate. In a recent WUWT thread on the retirement of the head of the green climate fund I did some quick bio research and concluded I did not like to be represented by that guy. Some time back we corporately lost a court case when the majority judge who had been president of a green group expressed unquestioned obedience to a UN treaty, this on World Heritage. I could give more examples of the nature of top participants in the climate business having led lives so unusual that you wonder if they have a chip on the shoulder that they seek public forgiveness for because of their 100% dedication to causes that were initially unpopular. Do you see any similarities to your people in similar positions? Extremely odd lives is how I would summarise, even anti-social with hostility to those who would criticise, plus extreme gullibility.
Sorry, but you have found one of my hobby horses. Geoff.
Very interesting thoughts Mr. Smith – thank you.
When I compare recent generations to my father’s generation, aka the Great Generation, it is clear that the population is getting much stupider. Based on fundamentals, this will continue until we have a Darwin event and the stupidest die off.
The Great Generation fought and won WW2, won the Peace, and then won the Cold War. This enabled the current feeble-minded generations to flourish, and the Millennials and the Snowflakes are the culmination of this regressive process.
I recently posted this premise. It does not JUST apply to global warming alarmism – it applies to all the many manias of the idiot political left.
“Global warming hysteria is promoted by scoundrels and believed by imbeciles.”
– Allan MacRae
“go back to being hunter gatherers” – tacit admissions that they are in fact too stupid to live in an advanced technological society”
Wait a second. You need a great deal of very specialized local knowledge and a lot of health, some strengths and substantial luck to survive as a hunter-gatherer. Moderns who temporarily try survive in such a lifestyle quickly discover they can’t hack it even for very short periods.
Ditto for being a peasant farmer. People who have lived in rural areas where people hunt and grow some of their own food slightly understand this–but urbanites hardly ever have even a clue.
Yes, if they cannot order it online with an app they don’t know what to do next.
Leo Smith,
Thank you. That’s whole piece is probably the best description of the current state of mankind’s intellectual capacity and its usage that I have read. In it, you said:
“In other words stupidity and incompetence and groupthink are natural things. It is only necessary for most people to know how to procreate. And no one likes Cassandras. Only when the chips are down do we value the competent and the super competent. And generalised incompetence leads eventually to the chips being down.”
That goes right along with another of my favorite quotes that Severian said here back in 2009:
“I’ve made the observation many times that no civilization or culture seems capable of surviving prosperity. It seems to allow these kinds of inanities to run loose unchecked, people take their eyes off the ball so to speak when it isn’t a matter of day to day hardship and life or death struggles. Relaxation and freedom from want seem to breed complacency and immaturity.”
You have nothing to apologize for, and you have my thanks as well as the thanks of others. We have seen this movie before, those of us old enough to have seen it then and wise enough to remember our history, when our ancestors also saw this movie and told us about it.
My only quibble is that our concern about climate is a bit misplaced. Climates are determined by the weather and it is the weather that we live in and must survive today, in order to see tomorrow. Climates are also local, just like weather is local. Global ‘averages’ without ranges can, have, and will be misused by those who seek power over others. Weather is a damped-driven deterministic system that shows mathematical chaos. Conditions matter and conditions are almost never exactly the same in one location over time.
Excellent.
If I was Putin, I would have tried to get Hillary elected.
yeah she n he do an awful lot for “donations” from their “friends”
funny how the slushfunds become hush funds?
i read bummers started one of his own too
I dont think Putin gave much of a damn either way
endless tiresome “exceptionalism” gets pretty stale.
I found the article quite hard to follow because it jumped around in time. So I made a timeline. It helps (I think) to understand a lot, but not everything:
Jan 2015 – DNC leaks to Wikileaks start, but at a very low level.
Mar 2016 – John Brennan (Dem) makes friendly visit to Moscow.
Apr 28 2016 – The leaks have continued at a very low level.
Apr 29 – 425 emails are leaked. DNC notice suspicious activity.
Apr 30+ – Leaks continue at high level.
May 4 – DNC call in CrowdStrike.
May 5 – CrowdStrike install software.
May 6 – CrowdStrike identify “Russia” as hacker.
May 3rd week – Leaks up to ~1500/day.
May 25 – Leaks have continued at a high level since Apr 29.
May 26 onwards – No leaks
Jun 10-12 – CrowdStrike “cleanse” the DNC system.
Jun 14 – DNC announces the hack and blames Russia.
Jun 15 – First document (“opposition research”) released by “Guccifer 2.0”.
Jun 18-Jul 14 – Guccifer 2.0 releases more documents, damaging Hillary.
Jul 24 – Hillary starts to malign Russia.
Aug 25 – Hillary makes very aggressive anti-Russia speech.
Aug 30 – Harry Reid accuses Putin of attempting to rig the US election.
Oct 7 – Obama publicly accuses The Kremlin of cyberattacks on US election systems and the democracy itself.
“Oct 7 – Obama publicly accuses The Kremlin of cyberattacks on US election systems and the democracy itself.”
Obama was told about Russian hacking long before Oct 2016, yet he did nothing to stop it.
This was the planned insurance policy in they very unlikely event (in their eyes) that Hillary lost.
Excellent article.
I must put my hand up tho.. It woz me wot dunnit. I don’t run a firewall or any security/antivirus at all, so most mornings I have to brush off the entire Russian security alphabets, DNC party criminals (hi Hillary, how’s things lately?), FBI, CIA and the odd Islamic terrorist bomb complete with ticking timer, which are crawling over my laptop like ants and bouncing secrets to and from each other, just to get something done.. Gerroff! [swipe]..
/sarc
But it’s true, I don’t run firewall or antivirus. On that subject, I once bought McAfee. Worst decision ever! It would monitor and poke into everything you did, such as check every executable you run, even if you quit and ran the executable seconds later. It also couldn’t be paused or quit, unless I manually ended the McAfee task.
I might as well keep all the secret service alphabets using my ‘puter, since they don’t interfere as much, really.. 😉
This might be more convincing if the author deleted the implications that Hillary’s motivations and thought processes were a known fact. When I see that I lump the whole piece under ‘conspiracy theory ‘ as a matter of course.
Hillary’s motivations are very clear as demonstrated by her entire life actions.
POWER AT ANY COST.
That is supposition and suggests bias. When these things appear in a historical article it raises very large red flags – as in danger warnings, I should add, given the context.
We don’t need Baroness Von Pantsuit to provide a notarized affidavit admitting that the reason she had an illegal email server in her bathroom to cover up bribes that she was soliciting as SoS via the Clinton Crime Family Foundation to know that’s what was going on given all of the known facts. Her life’s actions speak for themselves.
You might rely on common sense – it is often the truest compass available.
Well of course it is a conspiracy theory! I look forward to the movie!
Directed by the guy that caused the Benghazi attack?????
I think he is busy planning on making another hateful video (see Susan Rice).
” To thine own self, be true ”
It’s hard to tell where or when people cross the line and start believing their own lies in their own self interest.
At different levels, there are unbreakable codes, and networks that are not available to the public. I assume that everything that is on the web is an open book. Everything.
Had some experience with birdstrike. Got a frantic call from someone in the company claiming a program I’d written was malware. Same network traffic from a scripted language was ignored, but flagged by a compiled one. So I’ll let you decide what that means.
Sounds like complete
BSmeaningless drivel to me.Scripted languages are executed by a host; “svchost” in Windows for instance. Start up Task Manager and you’ll see many processes from “svchost” well each of them is running a script. If you allow svchost to do anything, it can do everything!
But if you compile the program now it runs as “itself” and is not recognized by your anti-virus program.
Sorry, that is simply not true. Anti-virus scanners check all kinds of files including .EXE and .COM files which are almost always compiled. link
Technically compilation and interpretation aren’t necessary. I could write machine code, which wouldn’t be compiled, which would execute as a .COM but only to win a sizable bet. link
This is a report on a press conference that happened this week related to this subject: https://www.youtube.com/watch?v=EBILe_zFN-Y
This is a more full version: https://www.youtube.com/watch?v=odeiBxOYKmQ
Take it with reasonable skepticism, but worth noting imo.
I still believe that it was an inside job carried out by a person or persons angry about the way Bernie Sanders was treated during the primary.
Attribution seems silly in the first place. Malware code is no different than any other software, i.e., it’s bought and sold as a commodity.
So what if the original coder was Russian or a Russian speaker? All that gets you is the original coder was “Russian or a Russian speaker.”
I wish people would stop confusing *hacker* with *cracker*.
Yeah, not just you on that one.
Especially when they don’t come from Georgia:<)
Indeed. I’d say that the proper term should be computer cracker, akin to safe cracker.
PHEW !!!!! Quite a read.
Many,many interesting thoughts.
Lol, “he’s a nut, he’s a loon, he’s crazy as a coconut”
More importantly for the standards around here, he was an anonymous coward for a long time.
I have no idea what that is supposed to mean.
Philip Schaeffer
I have no idea who “he” is supposed to be. I have no idea whose words you are quoting.
Finally, the “standards around here” don’t say a single word about “cowards”, anonymous or otherwise.
Philip, you’re bucking for permanent moderation with this ugly anonymous scattergun BS.
w.
So I buy a set of carving knives from Walmart. I give those to my daughter as a present. She uses them for a while but finds better knives and buys those. She then sells her Walmart knives at a yard sale. A woman buys the knives from that yard sale and takes them home. Two weeks later that woman’s 15 year old son uses one of the knives to kill the neighbor’s teenager who had been bullying him.
Headline: “15 year old uses knife bought at Walmart to commit murder”
Reaction: “Walmart guilty of selling knives to 15 year olds.”
excellent analysis, thanks for doing the heavy lifting and putting it all together
The assessment that jihadi groups may be implicated in the hack is significant. The house have also been suffering from an ‘IT’ debacle where a family of related staff from Pakistan have been running around congress making thousands of unauthorised accesses to congressional accounts. At one point an entire server went missing! Key individals have since fled to Pakistan. Debbie Wasserman-Schultz was seen threatening (and screaming at) police to recover a laptop held as evidence in the case. More at https://www.nationalreview.com/2017/07/debbie-wasserman-schultz-pakistani-computer-guys-bank-fraud/
and all over the web.
The devil is in the detail here, and I don’t know if one can legitimately join these two particular dots.
But here is some speculation anyway. I can imagine that DWS would have a good reason to lose her composure if she thought she had lost evidence which would confirm that democrats had been hacked by Pakistan, not Russia, and that the trigger for the Mueller enquiry was false.
The most interesting detail in the Pakistani family IT case (the lead figure employed most of his family in the IT work at a salary that I would be happy to live on) is that all charges against his wife were dismissed, and he pled guilty to one count of lying on a loan application. The only rational explanation I can think of is that he has been given a slap on the wrist in exchange for providing evidence about something else more important.
Or in exchange for not revealing something more important.
The stench of the Obama/Clinton abuses of power is overwhelming.
Interesting piece. The whole Obama/Clinton situation has gone to a point where Shonda Rimes would consider the plot incredible.