Original full article available here: Cyber security and critical infrastructure
Lars Schernikau: Energy Economist, Commodity Trader, Author (recent book “The Unpopular Truth… about Electricity and the Future of Energy”)
Details inc Blog at www.unpopular-truth.com
Imagine this…you wake up one morning, and the power is out. No lights, no heat, no phone charger. Not resulting from a predictable storm, or a run-of-the-mill downed line…just silence. The culprit? Someone behind a keyboard halfway across the world.
It’s not sci-fi. It’s not a drill. It’s a growing possibility.
Firstly let´s thank Nikola Tesla for his vision of Alternating Current (AC), a system that could send electricity much farther, more efficiently, and at higher voltages than ever before…the same AC that made the modern energy grid possible which today forms part of what we call critical infrastructure.
We have admittantly come a long way since then, and it’s time for us to chat about the risks of cyber attacks on our critical infrastructure.
Smart power systems are getting riskier
Yes, digital tools help utilities control and monitor everything from solar panels to massive transmission lines. But on the flip side…every connection is a potential point of attack. As energy infrastructure becomes more high-tech, it also becomes more exposed to cyber attacks.
In fact, millions of solar inverters, possibly compromised through software loopholes, have recently been flagged by researchers. Also consider that cross-border power cables, like the one between Finland and Estonia, have already been caught in the cyber crossfire… the risks are more often becoming a reality. So what are we going to do to mitigate these identfied risks?
What’s really at stake here?
This isn’t just about flickering lights or charging your phone a little slower. It’s about critical infrastructure… the infrastructure that keeps hospitals running, factories producing, and cities alive. A single targeted attack could create chaos across entire regions. In my latest blog – Cyber Security and Critical Infrastructure , I list some of the events for background on the magnitude of such attacks.
And as the energy world leans more and more on digital tools, and on decentralized power systems like solar and wind, the looming risk keeps growing.
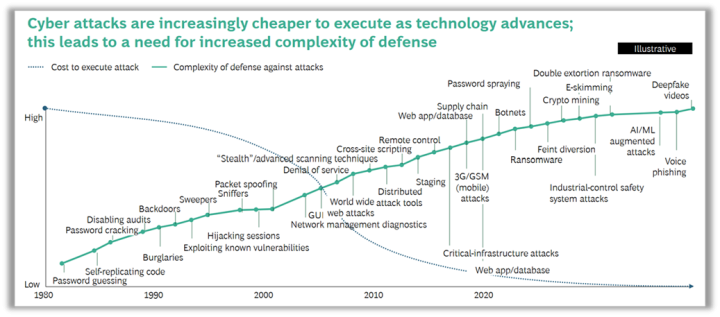
Cyberattacks become cheaper and require more complex defense | Source: BCG Executive Perspectives
The quiet race you didn’t know you’re in
While we scroll, stream, and charge up, there’s a behind-the-scenes scramble happening between nation-states, hackers-for-hire, and infrastructure operators. Everyone’s racing to either protect or penetrate the digital veins that keep energy flowing.
Some countries are already embedding cyber-resilience into their grid planning. Others? Not so much. The scary part is how uneven the defenses are, especially when the systems are interconnected across borders.
In other words, it doesn’t really matter if your local utility has top-tier cybersecurity if their upstream partners don’t bother. One weak link, and the whole chain shakes.
The conversation about cybersecurity in the energy space isn’t just for engineers and policymakers, it’s for all of us. If you’re curious…or a little alarmed, the full breakdown is worth your time. Read the full post here: Cyber Security and Critical Infrastructure


Specifically why are process industries (water, power, O&G, … list is long) putting their process control machines exposed to the Internet?
I do hope they follow the Purdue Process Control Model and keep Level 3 and below off the internet all the time, no exceptions.
This is my view, and has been for decades. There should be a separate communication network for government and for essential services. Exposing them to the world is outright insanity.
Exactly right!
While a separate network could still be hacked, at least the hacker would have to be in the country.
Yes, but the sepate network would not be accessible from absolutely anywhere, as an internet connection is by design. The limited access points would be much easier to monitor.
As an aside, my brother is a self employed chemical engineer who designs and implements process control software for water and wastewater systems–mostly industrial, I think. I know he can do this work from his office or home or wherever he and his computer are. I have been with him when he has made adjustments to processes and their chemical inputs to tweak the process.
If he can do this from wherever he is, it would seem the system is less secure than it ought to be.
That’s the problem: Easy internet access.
A safe alternative is for your brother to drive down to the water plant and make his inputs there. That’s less convenient than doing it from home over a computer, but it is hacker-proof. If they don’t want to be hacked, then don’t enter the internet environment.
And there are hackers out there who can find their way through just about any defense.
China is training hundreds of thousands of them, and there is bound to be a few that stand head and shoulders above the rest. It only takes one good one.
Way back when, there was an infamous hacker who was very good at what he did, but he was surprised when he found out that a Whitehat hacker had infiltrated his secure chat room and was seeing everything he and his buddies were talking about. The only way he knew the Whitehat hacker was there was when he introduced himself to them one day. Surprise! Surprise!
The best way to defeat superior internet hackers is to cut them off from your hardware. If you are on the internet, they might just get through to you, catastrophically. They might already be sitting there lurking, and waiting for the time to strike.
The worst thing happening is cloud computing. There is a huge incentive for business and government to move mission critical tasks to “The Cloud”. They can save massive amounts of $$ in equipment and knowledgeable staff salaries. I’ve seen this happen steadily until a disaster happens in “The Cloud” and brings the system to a screeching halt. Talk about a single point of failure! It’s probably the stupidest thing one could do, yet process control, hospitals, fire stations even trains, airplanes and cargo ships are managed in “The Cloud”. When was the last time your system in “The Cloud” published the results of the annual Penetration test? A comprehensive PEN test is not cheap and the local fire station wouldn’t even know what it means until they get clobbered by ransomware.
For some reason the researchers left the cloud connected Chinese grid-tie inverters off the list. One Chinese maker Deye just bricked inverters being sold in the wrong territory by sending a code to activate a preinstalled block on production with a message to either buy or code or buy the correct Branded inverter for the territory.
I wouldn’t trust any Chinese hardware. The Chinese are going to be bugging everything they make.
I thought they already are bugging everything, including their electric cars.
Imagine the situation in the UK, perhaps a few years from now.
A cold spell in winter, wind is generating <5GW, solar effectively zero, gas and other sources are insufficient to meet demand so we’re reliant on imports from Europe for the remaining 7-10GW when the interconnectors go down, maybe cyber, maybe direct sabotage (bombs), maybe political reasons, maybe the energy just isn’t there in the first place.
Not good news for all those relying on heat pumps, admittedly gas boilers won’t work either, but they at least are more flexible when the power does come back on, and frequently have separate gas fireplaces that can keep at least one room habitable.
I think it’s more a case of when, not if.
“The culprit? Someone behind a keyboard halfway across the world.”
The punishment when caught- the electric chair, ironically. 🙂 (and it should be green energy so they won’t mind so much)
From the article: “And as the energy world leans more and more on digital tools, and on decentralized power systems like solar and wind, the looming risk keeps growing.”
Our power grids should disconnect from the internet, which will neutralize internet hackers.
We had working power grids before the internet was invented. Power grids don’t need the internet to function.
In fact, *all* essential infrastructure like water purification plants and other things should also be disconnected from the internet.
We need to learn to do things a little differently. The Internet has made us lazy.
Not so much lazy as subservient to the accountants and lawyers who cluelessly manage the infrastructure.
Good information.