Correspondence Began Same Day He Rejected Invitation to Debate
FEBRUARY 24, 2012 – The Heartland Institute today released all the emails Pacific Institute President Peter Gleick sent to The Heartland Institute for the purpose of fraudulently obtaining internal Heartland documents. The emails can be found at Fakegate.org.
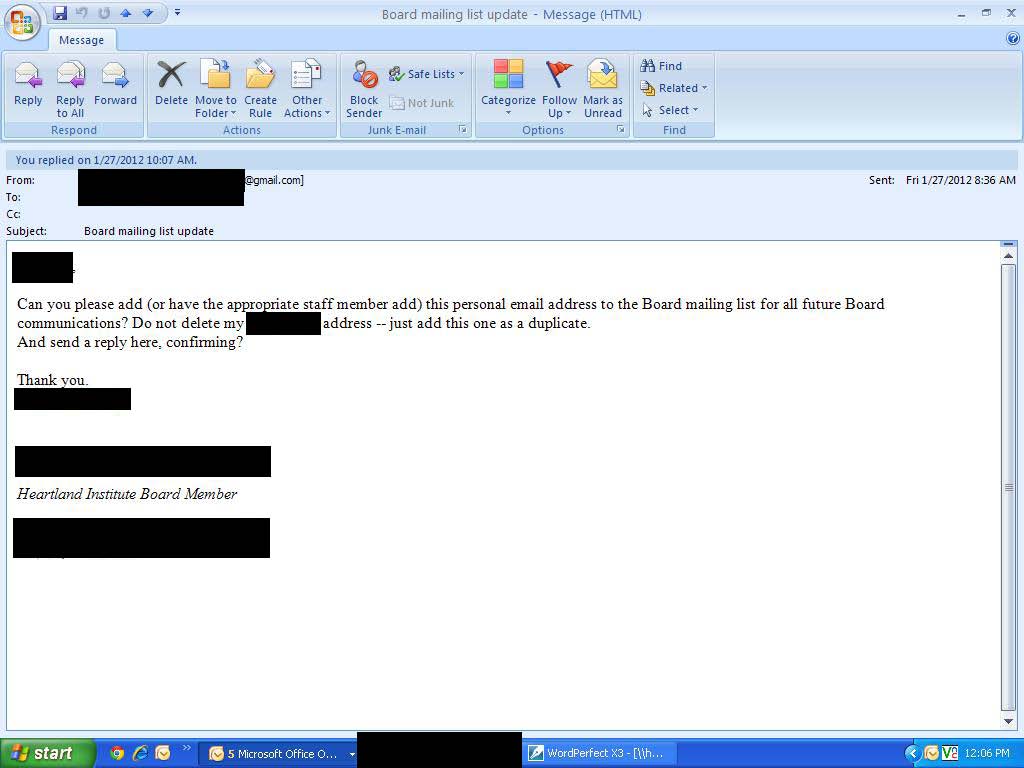
The emails reveal how Gleick “phished” the documents by stealing the identity of a Heartland board member, an act to which he publicly admitted in his February 20 Huffington Post confession. Minor redactions have been made to the emails to protect the individual privacy of those involved.
Gleick originally portrayed all of the documents he circulated, including the fake climate change strategy memo, as originating from Heartland. Now he claims he received that memo from an “anonymous source” before his theft. But the emails Heartland released today reveal Gleick never asked for either of the two documents that are specifically cited and summarized in the memo, suggesting the memo was written after, not before, he received the phished documents.
The newly released emails also reveal the first email from Gleick to Heartland was sent on January 27, 2012 – the same day he rejected a cordial invitation to debate climate science at The Heartland Institute’s 2012 anniversary benefit dinner in August. Email correspondence between Gleick and Heartland Institute Director of Communications Jim Lakely can be found here. That correspondence makes it evident Gleick was aware of Heartland’s policies concerning the confidentiality of its donors.
We repeat our request that the fake climate change strategy memo be removed from Web sites and blogs such as DeSmog Blog, Think Progress, and the Huffington Post, along with documents that were stolen from Heartland. It is the ethical thing to do.
Previous press releases from The Heartland Institute plus links to dozens of news reports and commentary on Gleick’s transgressions can be reviewed at Fakegate.org.
###
Here is a screencap from one of the email sets, click to enlarge:
more at Fakegate.org.
Classy/
I describe Al Gore’s justifications for bizarre actions concerning climate his “Broken Moral Compass.” There is a chapter about same in Don’t Sell Your Coat.
Gleick’s actions, seen up close in the e-mail presented here, are chilling. Almost enough so, but not quite, to make me not want any more popcorn.
This is pretty shocking stuff, and the requesting of contact info for the whole board tells us he had bigger plans in mind than just uncovering the info behind the “Strategy Document”. However, I’m a little shocked that Heartland would just take at face value that this was an legitimate board member request. I would have expected policies to be in place to contact the board member directly to confirm that the request was legit, or at least send all communication to both email addresses simultaneously.
The phishing tactics are almost on a par with those of wealthy nigerians …
The revelations here are just shocking for someone as supposedly “bright” as Peter Gleick. I hope they prosecute him to the full extent of the law.
RE: Phishing
The company I work for requires all employees to complete an online phishing awareness training. Phishing is a REAL threat in the business world today, and with a few easy steps (e.g. examining closely any embedded links in e-mails, and e-mail addresses of individuals), you can thwart most phishing scams. Be particularly wary of anything related to online financial transactions, such as Paypal, your personal bank, Amazon.com,etc.
This was no spur of the moment act of anger or revenge but systematic and deliberate fraud over a period of 14 days.
I don’t see how he can get away with this.
Given this info, I think Gleick can easily get off with a temporary/permanent insanity plea…
Looking at the emails and the attachments, it would be no problem to exclude the fake memo.
Just count files received by Gleick and what later emerged.
His lawyer must also be drinking the green coolaid, if he 1.) thinks Heartland is afraid of discovery, and 2.) thinks he is going to get fishing license in a criminal case against the victim.
oh dear!
he has admitted impersonating a board member, here is the evidence that he did this.
Over several days (not spur of moment) I have heard that the law is rather more forceful in the USA than perhaps the UK on this sort of behaviour.
I hope Peter Gleick is getting some veryvery good, rational advice from somebody..
Ie *IF* somebody sent him a fake document, he has no obligation to that person at all !!
and to assist Heartland in this.
If he knows who was involved in the creation of the document (hopefully not Peter, but very many people only thought of him, because of it in the first place) is to confess all now, apologise.
seek making reparations (very publically) and hope that Heartland would be satisifed..
If there was a MAJOR, MAJOR correction very publically, possibly might avoid a civil damages case?
Just my thoughts… Proper lawyers required on this now…
I have to watch an online video at least once a year about this kind of phishing attack. Surely Heartland has updated its internal security policies and training now.
This is a teachable moment for everyone. The weakest link in security is always the human factor.
If I’m reading this right, Gleick created a fake gmail address, and it seems that Heartland wanted to highlight that fact. Heartland screwed up by not having a policy of no confidential documents to webmail addresses. This wasn’t exactly high-tech hacking.
There’s a lesson for everybody here: email is insecure. No confidential documents should sent unencrypted. Period. Secretaries shouldn’t be authorized to hand out keys. Period. Even if Gleick phished this, an encrypted payload would have been useless to him. The keys need to be treated like … keys. Handed out on a need to know basis by the IT guy. In person. Only.
Calculating.
Obsessed and possessed.
Screwed.
What he said.
I keep reading this:
“But the emails Heartland released today reveal Gleick never asked for either of the two documents that are specifically cited and summarized in the memo, suggesting the memo was written after, not before, he received the phished documents.”
And I don’t quite follow the logic. Maybe I’m just feeling dense today – could some kind soul help me out? TIA
Interesting…by my count, he held back one pdf (the resume) in his document dump.
Of course, the IRS form and the forged memo aren’t anywhere to be seen.
Love the use of parenthesis and commas in that first email. Someone needs to add that text to the opensource project…
Why do I have this ominous feeling that Anthony knows way more than is being posted. All the posts betray that Anthony et al are playing chess when the greens assumed they are playing hop scotch….bad assumption.
I read ostensible “breaking” news here and it is all slightly stale news in reality for those in the know. I do understand why the news needs to be released is such a controlled fashion.
Gleick made the one mistake so-called geniuses always make, he thought Anthony et al were dumber than him. Turns out, the Heartland guys did everything right and let Gleick ravel himself…Gosh… though chilling are the fake emails, I almost pity the dumb-@55.
He’s been caught, hook line and sinker and Heartland gave him every opportunity to behave ethically. There is an Aesop’s fable for this…
The Frog and the Scorpion.
Gleick did this because in the end, it is within his nature to do it.
Hmm, aren’t there laws against identity theft?
It appears that the email requesting confidential board member information meets the criteria for proof of the crime of cyber impersonation under CA law. Criminal wire fraud under federal law also seems evident.
It is time to compose a farewell hyku for Peter Gleick. How about a contest, Anthony?
Jean Parisot says:
February 24, 2012 at 10:36 am
His lawyer must also be drinking the green coolaid, if he 1.) thinks Heartland is afraid of discovery, and 2.) thinks he is going to get fishing license in a criminal case against the victim.
________________________________
….. or a civil case. It’s probably a scare tactic to imply that there’s going to be a big fight. Like the opening scene in Gladiator …. and it will end the same way. There’s no defense here.
My oh my, are those e-mails vile. This freak wants to save my planet ??
Mosher commented on that. In fact, that’s what led him to Gleick. I’m not seeing what’s so unusual. Can someone point out exactly what’s so unusual/idiosyncratic?
Anthony, Heartland gets a win on this eventually, but the Greens will not underestimate you guys again. They will regroup and lay a trap for Heartland.
In his “confession”, Gleick says that he did not alter any of the documents he stole from Heartland.
However, one of the files that HI sent to Gleick was called Binder1.pdf. The version on DSB is called Binder1 (2).pdf
That (2) is added when you open a pdf, make changes, and then save the changed document to the same directory as the original.
Also, Gleick was provided the minutes of the Jan 17 board meeting, but he did not include those in the slur package to his “15 friends”. Surely there is a reason for that. One wonders what exculpatory info was in those minutes …
Did anyone else experience a cold damp skin crawling sensation when they read the emails? It was caused by the cold-blooded dishonesty of Gleick’s politeness toward the HI staff members.
Yuck.
The CAGWist’s got themselves a real sick ‘hero’ there.
John