Correspondence Began Same Day He Rejected Invitation to Debate
FEBRUARY 24, 2012 – The Heartland Institute today released all the emails Pacific Institute President Peter Gleick sent to The Heartland Institute for the purpose of fraudulently obtaining internal Heartland documents. The emails can be found at Fakegate.org.
The emails reveal how Gleick “phished” the documents by stealing the identity of a Heartland board member, an act to which he publicly admitted in his February 20 Huffington Post confession. Minor redactions have been made to the emails to protect the individual privacy of those involved.
Gleick originally portrayed all of the documents he circulated, including the fake climate change strategy memo, as originating from Heartland. Now he claims he received that memo from an “anonymous source” before his theft. But the emails Heartland released today reveal Gleick never asked for either of the two documents that are specifically cited and summarized in the memo, suggesting the memo was written after, not before, he received the phished documents.
The newly released emails also reveal the first email from Gleick to Heartland was sent on January 27, 2012 – the same day he rejected a cordial invitation to debate climate science at The Heartland Institute’s 2012 anniversary benefit dinner in August. Email correspondence between Gleick and Heartland Institute Director of Communications Jim Lakely can be found here. That correspondence makes it evident Gleick was aware of Heartland’s policies concerning the confidentiality of its donors.
We repeat our request that the fake climate change strategy memo be removed from Web sites and blogs such as DeSmog Blog, Think Progress, and the Huffington Post, along with documents that were stolen from Heartland. It is the ethical thing to do.
Previous press releases from The Heartland Institute plus links to dozens of news reports and commentary on Gleick’s transgressions can be reviewed at Fakegate.org.
###
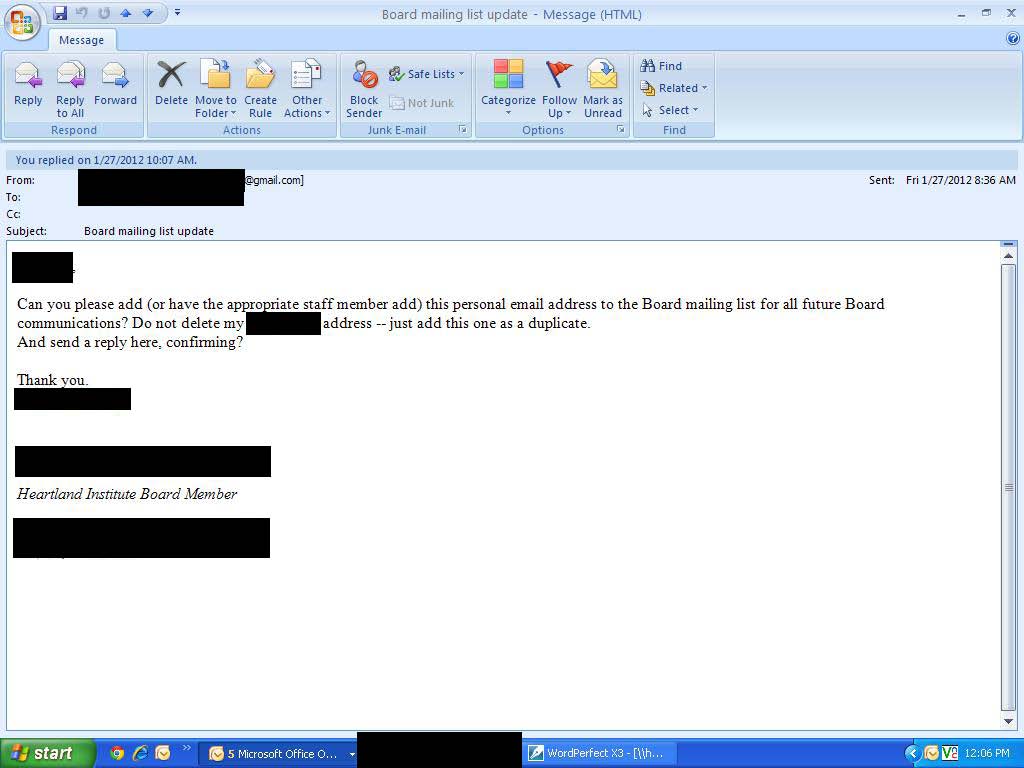
Here is a screencap from one of the email sets, click to enlarge:
more at Fakegate.org.
One can only hope that charges are brought so that all of Dr. Gleick’s computers are seized for a thorough forensic examination. I hope that one of the attorneys reading this will opine on the extent of the Pacific Institute’s exposure should he have done this on the PI’s time and equipment. He is the founder of the PI. I suspect that every computer that he uses has a PI property tag on it including any laptop or home based tower that he uses. If a search and seizure was appropriate in TallBloke’s case, it seems even more so in Dr. Gleick’s case.
@Hexe Froschbein
It’s people who commit crimes, not the opportunities they have to be criminal…!
I agree, I do think that in his stupidity and arrogance he did not think this through. I have heard he has been ranting a bit lately. The amount of times in my life when I have been so adamant about something only to realise I was totally wrong, that moment can be painful. I wonder how many of these warmists are starting to get that feeling. Your entire career is on the line so thinking rationally is hard.
I get the feeling many of these guys are starting to re-appraise AGW. I guess they are checking every chart and table and they all saying nothing to worry about. It must be so painful.
I also think that Anthony knows a little bit more about this episode. Anthony can savour his moment as he’s been the target of lots of spite and hatred. Braver man than me.
BT, take a look on CIF, they think the fake is fact.
mpaul says:
February 24, 2012 at 11:21 am
How do we know that Gleick acted alone? Much of the narrative so far has assumed that Gleick was a lone wolf, acting on the spur of the moment — a crime of passion, it you will. Gleick’s “confession” was carefully crafted to leave this impression. But this email suggests that Gleick had information that would take a bit of time to collect.
– – – – – – –
mpaul,
I have had similar impressions as yours that there is reason to question the presumption/impression that Gleick was/is the sole actor in the HI hoax/fraud.
First point is psychological in nature. Does Gleick appear to be a ’cause’ groupie activist cum scientist or does he have the personality of a strongly independent think-for-himself personality. I go with the former. He would share the idea of what he was planning on doing and share the triumphs along the way with fellow ’cause’ members. I suggest he would wildly celebrate with fellow cause members on these two occasions:
So, investigation of the time period immediately following those two dates might be fruitful. I highly recommend looking for a disturbance in the Farce (‘cause’ community) during those periods.
Second point is the tight interconnectedness we know exists in the community supporting the ‘cause’. They are an efficient nexus. Gleick knows they support attacking skeptics. How could Gleick refuse such a proven and willing tool to use for his efforts?
I had a dialog with Lucia yesterday at her BB about doubting Gleick was a lone actor (lone wadi) in the HI hoax/fraud.
John
I take it that you’ve seen Desmogblog’s latest offering?
http://www.desmogblog.com/heartland-selling-out-science-school
So he collects these documents over a period of two weeks, and sits on them for another half week or so before disseminating them? This is about as pre-meditated as it gets, and I would not be at all surprised if there are discovered conspiring parties involved. It has the feeling of an immature person who, once they have succeeded at something naughty, keeps pushing the envelope to see how much they can get away with – perhaps bragging secretly to their friends all the while, who may egg them on further. I would sleep better at night however if it were truly just him acting alone.
My favorite part is the bottom of the Feb. 3rd, 10:38 am email…the confidentiality note. I think all this, combined with his established awareness of their policies regarding donor privacy, are definitely enough to constitute a case for malice:
He knew what he was doing, he did it over a long period of time, he knew why it was wrong, and when the time came, he didn’t “leak” the information, but blasted it out to over a dozen (15?!) contacts sure to help with the defamation.
Anthony, Heartland gets a win on this eventually, but the Greens will not underestimate you guys again. They will regroup and lay a trap for Heartland.
Of course they will…. Anthony is a stupid TV weatherman after all! 🙂
Did Heartland offer him the opportunity to debate before or after he started pfishing?
John H asks: “How does discovery work in a Federal case where the US is the injured party compared to a civil case where Heartland would be the injured party ?”
I presume you’re referring to a criminal case as opposed to a civil suit. In a criminal case, the procedure is fairly simple: the prosecutor (or whoever is assembling the case) comes up with a list of places he thinks relevant evidence can be found, (ie, personal computers and files) he goes to a Judge and gets a warrant, and then a team of agents (if it’s a Federal case) execute the warrant and seize whatever they want. It is usually a fairly brutal process. In a civil case you have to ask nicely for the information, and then seek penalties if the other side refuses to provide the information. (such as a default judgment against)
As has been said several times, the issue of the forgery is important, and identity theft is significant. But the Big Bad here from Gleick’s POV is that his actions, the ones he’s already confessed to, clearly violate the Federal Statute against Wire Fraud, and that is a Federal Felony carrying a sentence of up to 20 years in prison and a large fine.
A Federal Felony is a damned serious charge to be up against, especially since Federal Criminal Courts have about a 95% conviction rate for cases that go to trial.
More to my previous comment wondering who else was invoked — I wonder if Gleick paid anyone to do the research that was necessary to carry this out? And if so, did he use federal grant money for that purpose? If he did, then we can add a series of additional criminal statues that were broken. And, such payments could put the Pacific Institute’s board members at risk of personal liability.
Further, if there is any evidence that one of the funding agencies had any kind of discussion with Gleick where they said something like: “it would be nice to establish that the skeptics are funded by Koch or big oil”, then that would provide the predicate for a Congressional investigation. The fact that EPA is being busy little beavers trying to remove public evidence of their connection to Gleick seems… interesting.
Paul Westhaver says:
February 24, 2012 at 10:55 am
“Gleick made the one mistake so-called geniuses always make, he thought Anthony et al were dumber than him. Turns out, the Heartland guys did everything right and let Gleick ravel himself…Gosh… though chilling are the fake emails, I almost pity the dumb-@55. ”
Do you want to imply that Heartland knew they were being phished when Gleick’s e-mail arrived there? I think that’s one level too paranoid.
Of course, they COULD have looked at the e-mail header which tells you the route the e-mail has taken; and probably they would have seen it came from California. Depends on their policies and care whether they did it… In that case they could have played Gleick knowingly… But I don’t think Heartland has the skills to have thought of that. They’re not an IT shop.
Morph says:
February 24, 2012 at 12:01 pm
“If this is the best and the brightest of libertarian thought then the “left” is perfectly safe.”
You said it. If.
Don’t. Think. So.
TerryS says:
February 24, 2012 at 11:19 am
Re: Michael Larkin
Thank you so much for taking the time and trouble to explain this to me, Terry. It’s much clearer to me now.
It appears he started phishing the very same day he declined the speaking invite (to the Heartland Annual Donor gathering).
In the email RSVP (and before) he was pressing for donor information, which Heartland declined with a list of very specific reasons.
This must have really pissed him off.
Heartland needs to be seriously careful in the way they release this information. It’s too late now, but full desktop screenshots are a bad bad idea. I can gather all kinds of information about the softwares they use there (looking for easy in) and at least one person that works there. I see they are using MS Exchange, or at least MS Outlook, so the MS Exchange is a high probability. They run Sage Software’s ACT! CRM (customer management software). They’re running RealVNC for remote desktop access, so I could attack that to get into their machines. I can also deduce, with a little Googling, that the person who’s machine is being displayed is interested in weight loss, based on the Internet Explorer title they’re browsing. If I were a shifty eyed character, I would find a WordPerfect exploit, wrap it up as a weight loss attachment for “42 Best Ways To Lose Stomach Fat Fast” and throw it at every Heartland email address I could find to see what sticks. All it will take is one interested employee (perhaps this one) to open the attachment and I’ve now got all of Heartland’s customer base from their ACT CRM, via VNC.
Seriously, if Heartland is having troubles with simple Phishing and Social Engineering exploitation, that will be nothing compared to giving away information about softwares like VNC, WordPerfect, Outlook/Exchange and ACT!.
Heartland and FakeGate.org need to consider a little more carefully what they release to the public. If they’re going to do screenshots, at least use the Alt+PrntScrn, so just the Outlook app would have been exposed.
mpaul says:
February 24, 2012 at 11:21 am
“On that last point, it would seem like there would be a reasonably high probability that the admin who dealt with this request would send a confirming email to the real email address of the board member along with the fake address.”
A request like this is not handled by an admin but by ordinary office staff; a secretary or similar, I would think. Well – I would set up a policy where suspect e-mails are forwarded to an IT savvy person for analysis, see above, but that would be me…
OUT, OUT, DAM E-MAIL DOTS AND CODES OUT I SAY….!!!
P. Gleick
@Paul Westhaver
“Heartland gets a win on this eventually, but the Greens will not underestimate you guys again.”
I disagree Paul. They’ll continue to understimate all of us. They have clearly got to the stage now of genuinely believing their own propaganda and will eat themselves – Gleick style – as a result.
Re: Jean Parisot
Heartland offered him it before he started pfishing. He might have even got the contact email address he used from the email inviting him to the debate.
Gleick seems to use Parentheses on parts of sentences that would ordinarily not be separated. Proper use of parentheses are for asides (something related, but not belonging in the same subject as sentence), or clarification (refer to this and my previous parentheses).
For instance, he has this in one of his e-mails to HI:
That doesn’t quite fit the use of parentheses. You could simply eliminate those parentheses and the sentence would read just fine.
I think Heartland is being quite cocky in their behavior thus far. They seem to be behaving as an organization that thinks they can pressure their legal opponents into a major concession. All these public releases of evidence on the internet are very unusual. I am not a lawyer, but I cannot remember the last time I watched a legal case in it’s infancy where one side was displaying so much detail of what happened before a judge was involved.
Well, if you look at the screencaps, you see no specific document requests. If Gleick were confident after having gained access to the mailing list that his address had been accepted as part of the group, and he were acting on the information that the faked document contained, why wouldn’t he ask for specific documents? Having dealt with boards of directors before, I would expect that requesting copies of past minutes of meetings or agendas would be no big deal, something a secretary would be “happy” to provide.
“Heartland needs to be seriously careful in the way they release this information. It’s too late now, but full desktop screenshots are a bad bad idea.”
– Seconded!
Chuckarama says:
February 24, 2012 at 12:34 pm
If I were a shifty eyed character, I would find a WordPerfect exploit, wrap it up as a weight loss attachment for “42 Best Ways To Lose Stomach Fat Fast”
That irritating little popup haunts me to no end. I have no interest in losing weight.
Fish taxonomists have just announced that the species currently known as the Northern Long-nosed Sucker will be renamed the Northern Gleick.
After learning of these details I am more convinced than ever that this was a setup. If they realized he was phishing it would have been so simple to feed him the fake document.
This whole affair is astounding. It’s a story that Hollywood would pay expert writers big bucks to conceive.
I guess bottom line for Gleick is if you can’t convince people in a fair debate, steal their identity and use that to steal their confidential papers to shame, threaten, and embarrass them. However, in a classic twist of good old fashioned poetic justice, Gleick fell on his own sword.
The CAGWsters are gonna get their due.
Something that is particularly galling here is that he should decide to do this immediately after the speaking invitation email exchange we have already seen. He’s treated so politely by the HI the only way I can possibly get into his mindset to understand why he suddenly decided the phishing would be a good idea is that he is so thoroughly convinced that HI and others ARE part of some enormous conspiracy – fuelled primarily by the usual suspects (Desmog, Guardian etc) who tell eachother the same things over and over and so therefore they must be true.
That such a senior and influential scientist could think like this is chilling.